The challenges of working remotely, COVID-19-related phishing attacks, a business-oriented perspective on cybersecurity and live penetration testing. The up-to-date nature of the Security First conference program was truly impressive—even for a security geek like myself.
See the subjective review of the Computerworld and ISSA Polska online conference.
Remote work vs. IT security
A remote conference on cybersecurity simply would not be complete without a discussion about remote work. At Sidnet, we have been running projects outside the main office for years—after all, our team members work remotely from various cities of Poland. The coronavirus pandemic has made our remote working experience even more vital in the eyes of customers virtually overnight. Everything points to the belief that the tendency to replace office work with remote work will continue in the coming years.
The future of cloud services
Michał Kurek confirmed that the COVID-19 pandemic is bound to further popularize cloud technologies. According to KPMG research, 43% of Polish companies already utilize cloud solutions with another 17% planning to commence using cloud services shortly.

Source: Security First.
A revolution in the work environment
According to Paweł Marciniak from Matrix42, the work environment is undergoing several changes, including:
- A change in the way work is perceived: a shift from work seen as a place to work seen as an activity.
- Changes in the needs of both employers and employees: a shift from fixed hours to flexible hours; from permanent employment contracts to freelancing and the gig economy; from hierarchies to dynamic organizational networks.
- A change in the approach to the company IT management: a shift from central management to employee self-service thanks to the access to remote systems and the knowledge on how to use them to continue the company’s operations from anywhere in the world.
Cybersecurity vs. business development
The relationship between IT security and business was a vital topic. It is astonishing just how often the first step to resolve a company’s technical problems is improving communication. However, this works both ways—removing technical issues can ease tensions at the company, e.g. in situations where the security department is perceived as an obstacle.
Stages of maturity in IT security management
Paweł Wojciechowski from Fortinet outlined the security challenges based on the company’s scale:
- The lowest level characterizes medium-sized companies with IT departments that deal with few incidents.
- The second level is a domain of medium/large businesses with dedicated security teams.
- The highest level of maturity is attained by the enterprise sector companies with dedicated Security Operations Centers (SOC), advanced processes and written rules of conduct.
Industrial network security (OT)
Learning more about cybersecurity challenges in the manufacturing industry, which uses both IT solutions and industrial networks (Operational Technology, OT), was certainly interesting.
Threats to the Industrial Control System (ICS)
Roland Kulanek’s presentation was meant to remind everyone that cybersecurity is a continuous process. In addition, a speaker representing Rockwell Automation also addressed some of the myths related to Industrial Control System (ICS) security. Any system—even if hidden behind a firewall or cut off from the Internet altogether—can become the target of an attack.

Source: Security First.
IDS and IPS systems—differences and applications
Wojciech Kubiak from PKP Energetyka explained when and why IDS and IPS solutions should be used. Wherever industrial (OT) and corporate (IT) networks coexist, using a hybrid system is necessary:
- An Intrusion Prevention System (IPS) is a solution that actively protects IT components, especially operating systems, databases and web applications.
- An Intrusion Detection System (IDS) is better suited to protecting OT components. It should passively monitor applications and control systems and search for any network anomalies.
IT security novelties
COVID-19 as phishing bait
The pandemic has generated anxiety, which increases the likelihood of making irrational choices, alongside the need to work and learn remotely—often with the use of private networks and equipment. Scammers have quickly begun exploiting this opportunity to launch coronavirus-themed attacks. Joanna Karczewska presented the scale of this phenomenon along with several alarming examples. What are the forecasts? It will only get worse unless we start employing proper security standards.
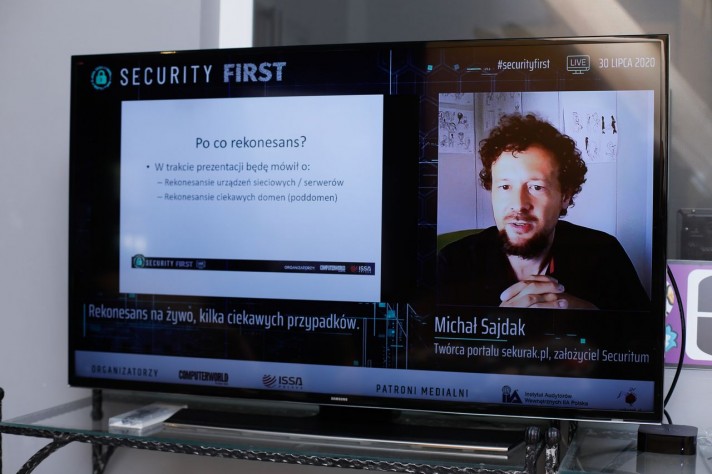
Live penetration testing
Michał Sajdak conducted a live reconnaissance of servers and network devices using penetration testing. I was particularly curious about this presentation, given that I follow Michał’s activity on the Sekurak.pl web portal and appreciate his factual, concise articles. The presentation itself was very similar in this regard.
Source: Security First.
Data recovery
Daniel Olkowski from Dell Technologies presented the idea of a digital bunker that allows users to recover data after an attack. What should you consider when making one?
- Isolate the digital bunker from the rest of the infrastructure.
- Retain deletion- and modification-resistant backups.
- Automate such operations as data retrieval, verification and recovery.
HP Sure security systems
I have been using Linux for years and typically do not stay up to date with the Windows software provided with most computers. Nonetheless, opening websites and attachments using virtual machines (HP Sure Click) is bound to protect many computers from malware. The HP Sure View Gen3 privatization filter built into a laptop screen was also a positive surprise. I will bear this option in mind when buying a new device.
